金三胖(gif)
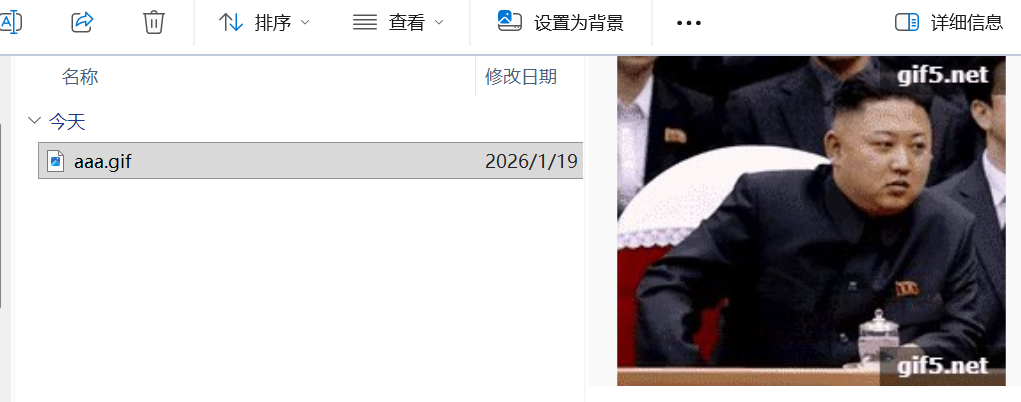
使用工具Stegsolve
File Format:文件格式,这个主要是查看图片的具体信息
Data Extract:数据抽取,图片中隐藏数据的抽取
Frame Browser:帧浏览器,主要是对GIF之类的动图进行分解,动图变成一张张图片,便于查看
Image Combiner:拼图,图片拼接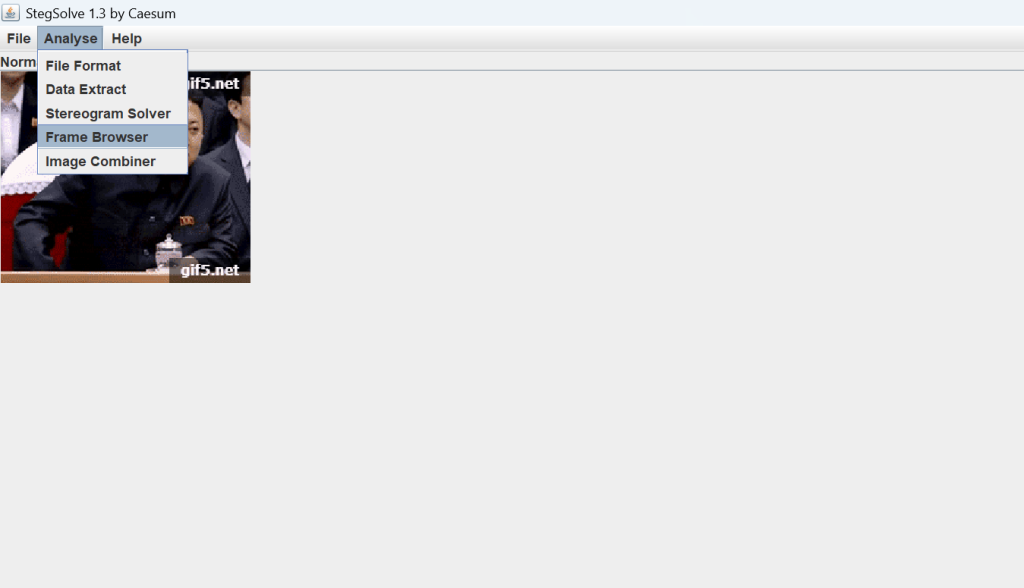


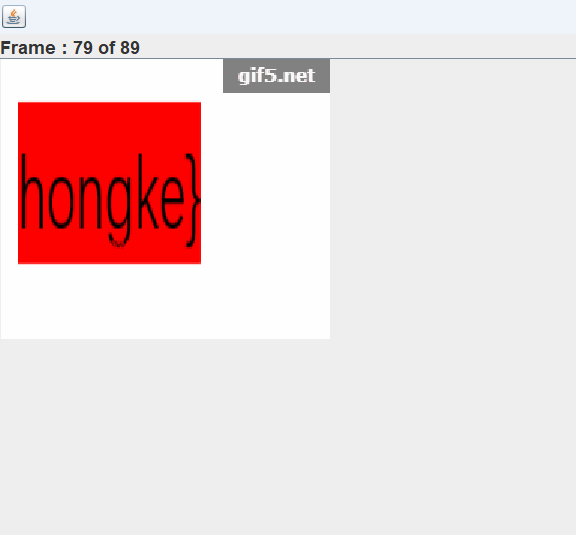
得到flag:flag{he11ohongke}、
你竟然赶我走
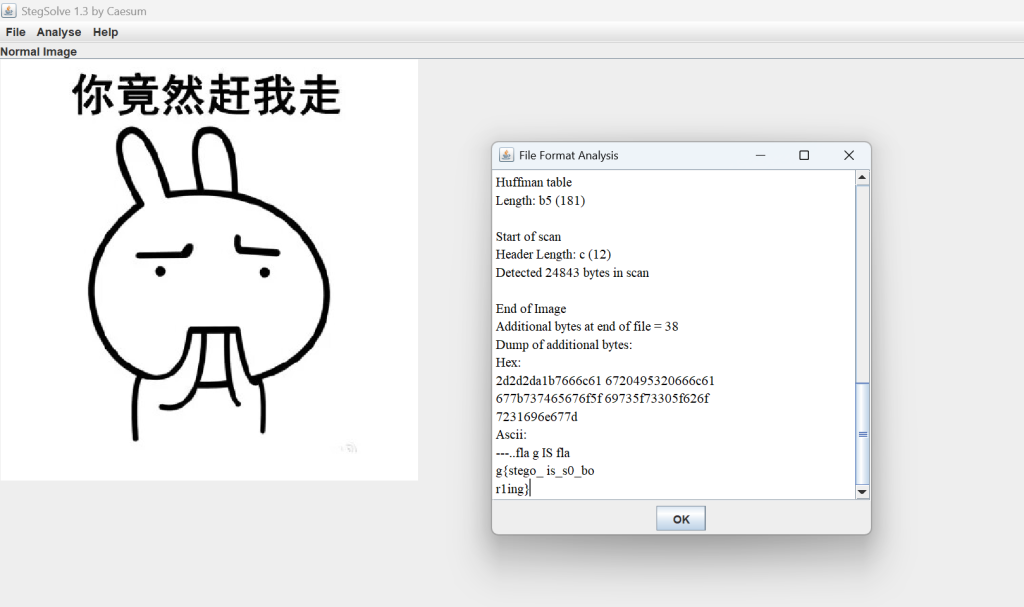
依然使用stegsolve,得到flag:flag{stego_is_s0_bor1ing}
二维码

给了个二维码png文件,先看下二维码里有什么
【注意对于1kb的图片文件还是可以隐藏内容的!!!】
找到89 50 4E 47发现后面50 4B 03 04经典的zip标志头,并且没有进行伪加密,直接粘贴到新的文件
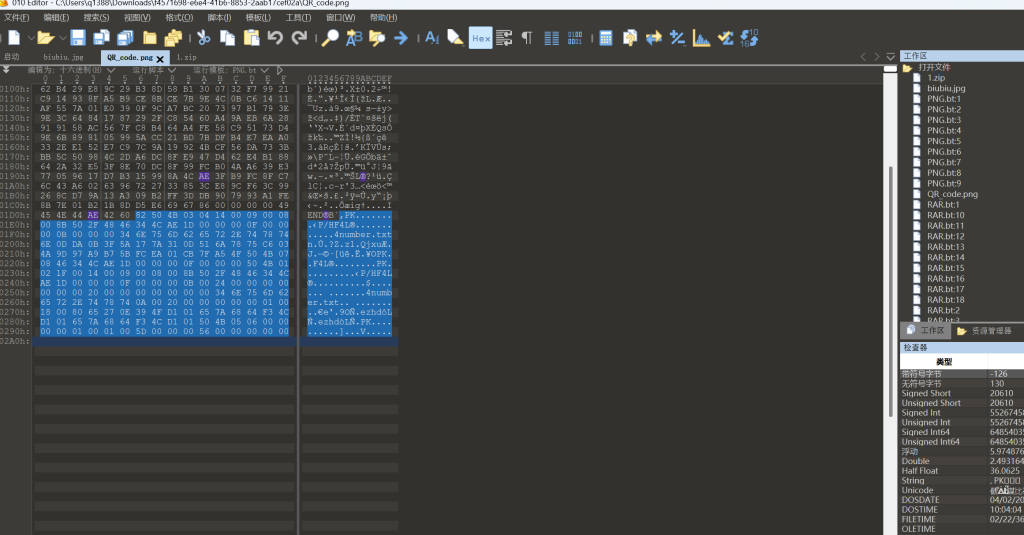
打开这个zip发现里面有个txt'文件,很明显,flag就在里面了,但是它加密了
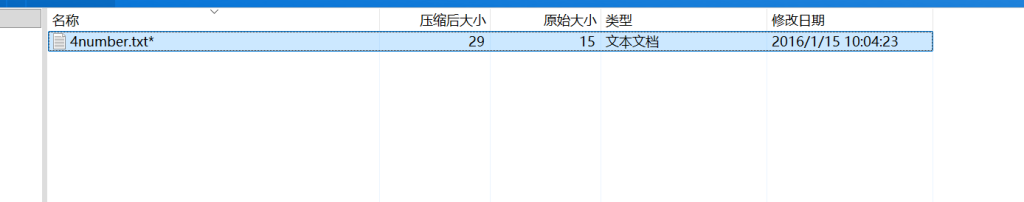
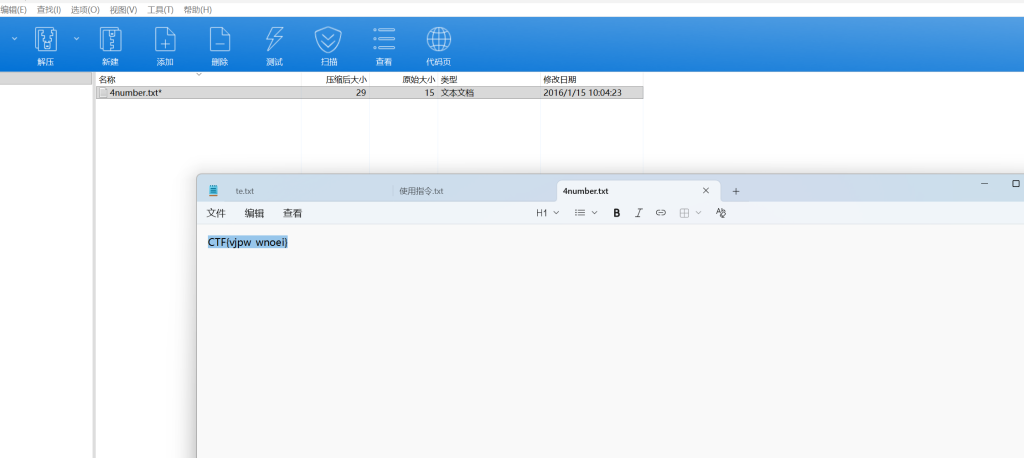
最后用ARCHPR爆破解出密码7639,打开txt得到CTF{vjpw_wnoei}(但是buu上提交格式是flag{},需要改下包装提交)
大白

由提示,很明显,是调整图片的高度
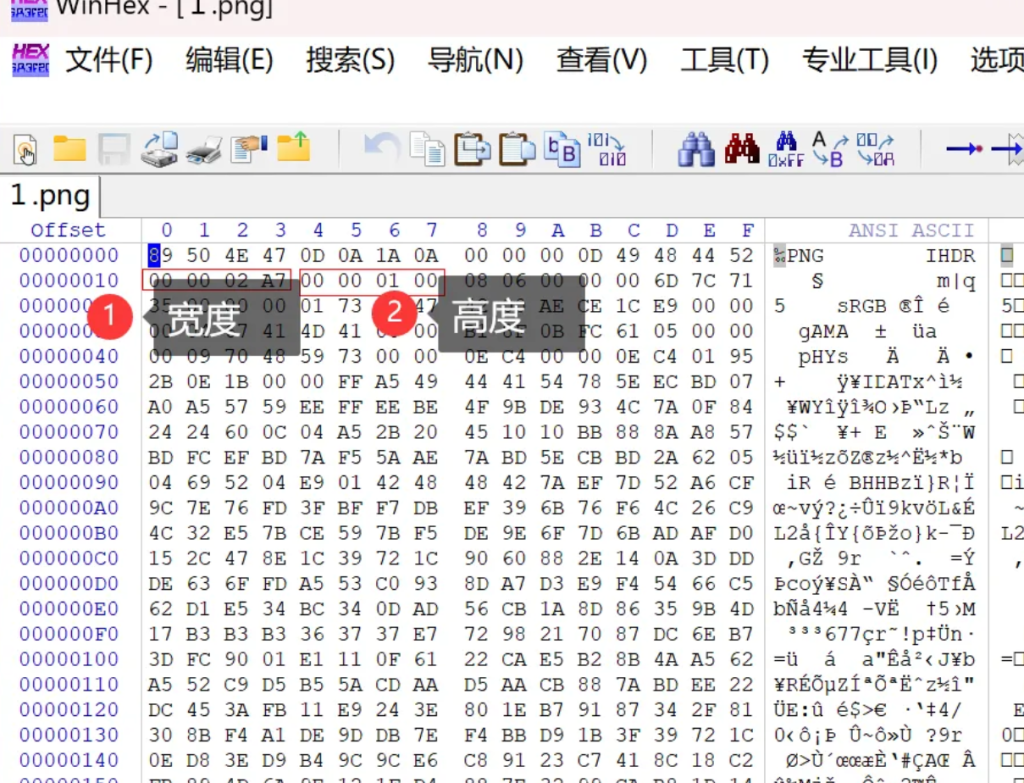
知识点:修改png长宽:
- 在IHDR块起始位置后偏移12字节处,找到宽度的4字节数据,将其修改为目标宽度的十六进制值(大端序)。
- 在宽度后偏移4字节处,找到高度的4字节数据,将其修改为目标高度的十六进制值(大端序)。
例如:若目标宽度为1000像素(十六进制00 00 03 E8),高度为500像素(十六进制00 00 01 F4),则需将对应位置的字节替换为这些值
此处将00改成F0

获得flag:flag{He1l0_d4_ba1}
Wireshark(流量分析)
题目:(黑客通过wireshark抓到管理员登陆网站的一段流量包(管理员的密码即是答案))
知识点:
"""
Frame物理层
Ethernet数据链路层
Internet Protocol Version 4网络层IPV4协议
Transmission Control Protocol传输层TCP协议
Hypertext Transfer Protocol应用层HTTP协议
"""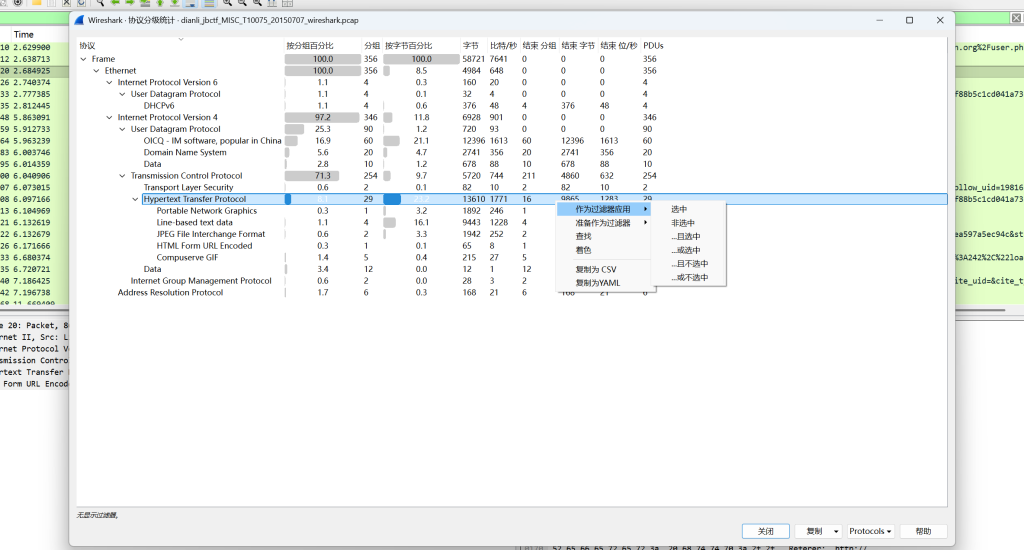
发现应用层HTTP协议占比最高,应该优先分析,优先分析占比最高的。点击右键滑到“作为过滤器应用”点击“选中”,再返回原页面,这样就显示过滤了HTTP协议相关的数据包,可以看见左上方的应用显示过滤器的输入框内容也添加了”http“,现在只有29个数据包了,我们即将开始逐个分析,点击每一个数据包,观察下面的窗口。发现第三个数据包的TCP/IP协议栈解析窗口和数据显示窗口处都出现了flag(password),将其复制,输入。
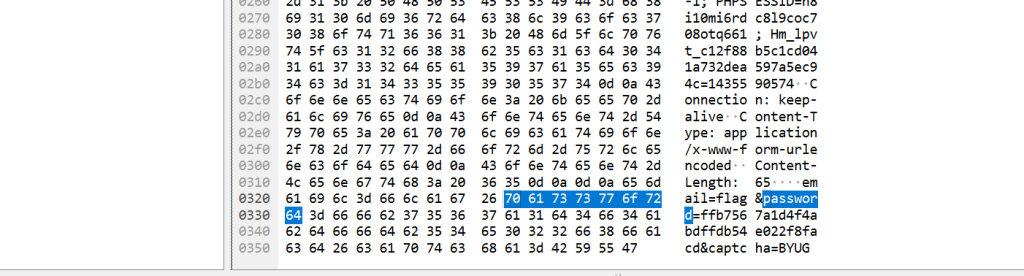
得到flag:
flag&password=ffb7567a1d4f4abdffdb54e022f8facd
--------------------总结下流量分析题---------------------------------
- 观察分组数(wireshark右下角),如果分组数量较大我们就进行协议分级进行分析,数量较小就逐个人工查看(数量小协议分级效果不明显,但还是可以优先协议分级减小工作量)。
- 根据协议分级的结果,我们优先分析数量多占比高的协议流量,分析过程根据题目不同思路也有所不同。
- 如果协议分级中有文件传输协议或是有传输媒体文件内容优先进行导出,一定要使用foremost工具进行辅助。
- 如果没有思路就搜索“flag”“ctf”等关键词。
- 涉及到攻击的流量就只能逐个追踪TCP流查看了。
乌镇峰会种图
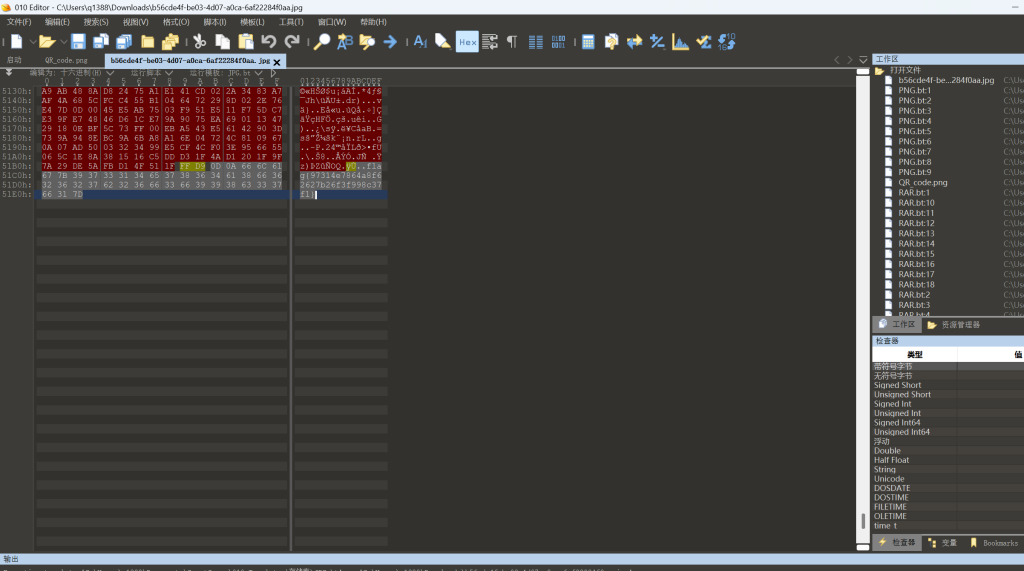
直接101editor查看,发现末尾flag{97314e7864a8f62627b26f3f998c37f1}
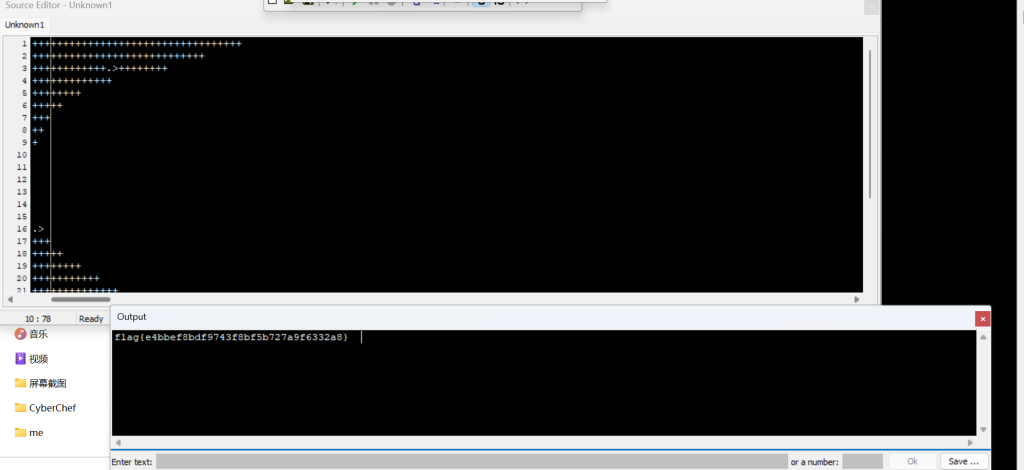
N种方法解决

给了一个exe文件,我们用101editor打开
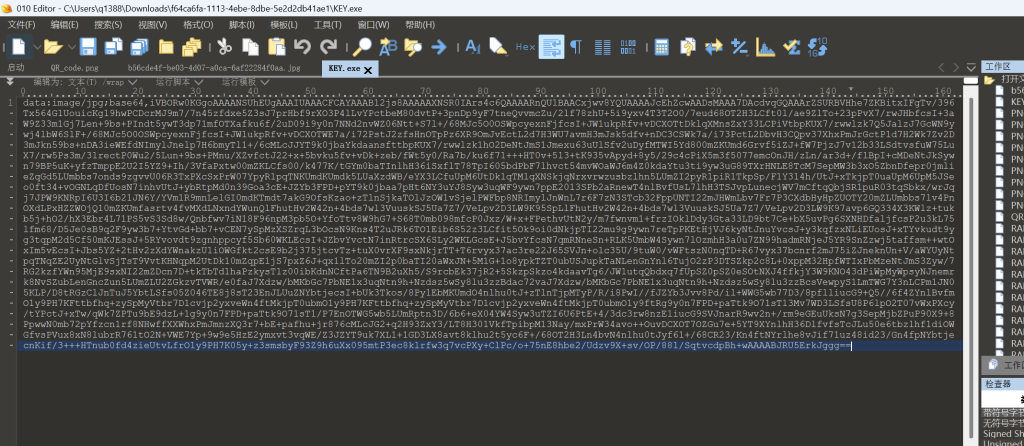
发现明显提示Base64,使用cyberchef解码,出来一个png文件,发现是二维码
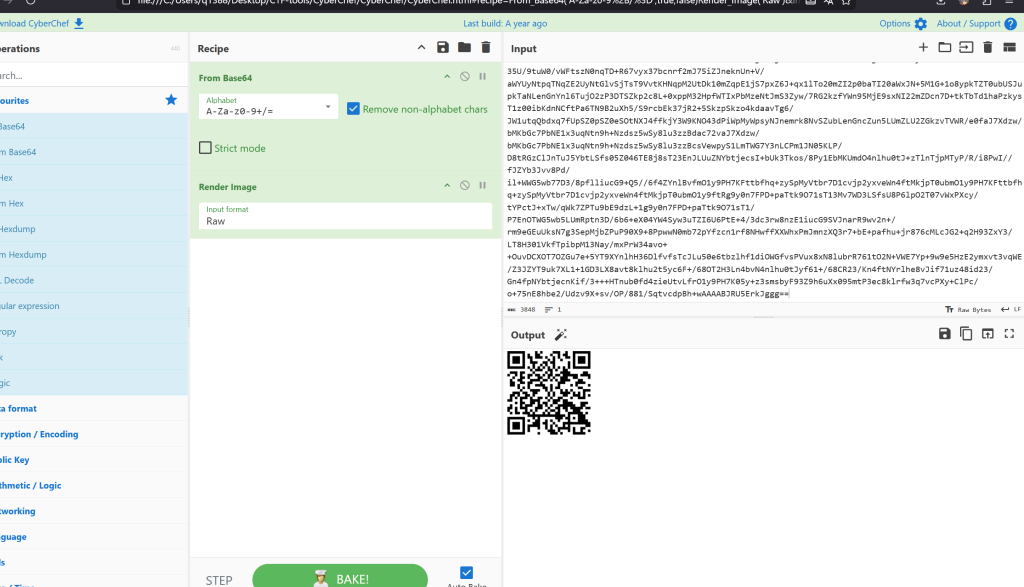
识别二维码,得出结果
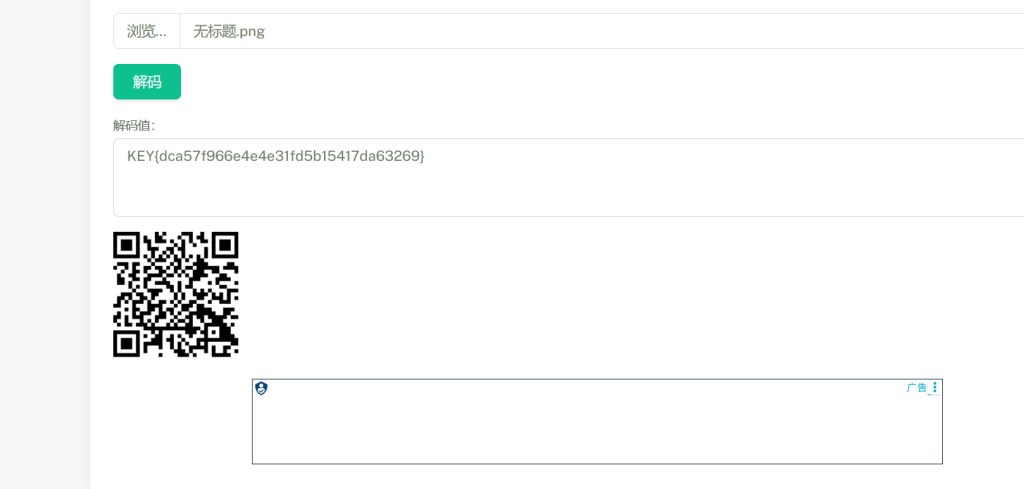
得到flag:flag{dca57f966e4e4e31fd5b15417da63269}
基础破解
(非常简单,自己看吧)

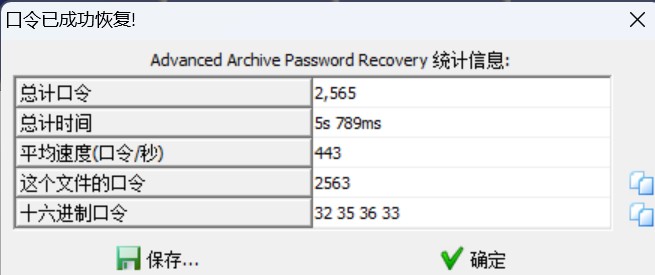
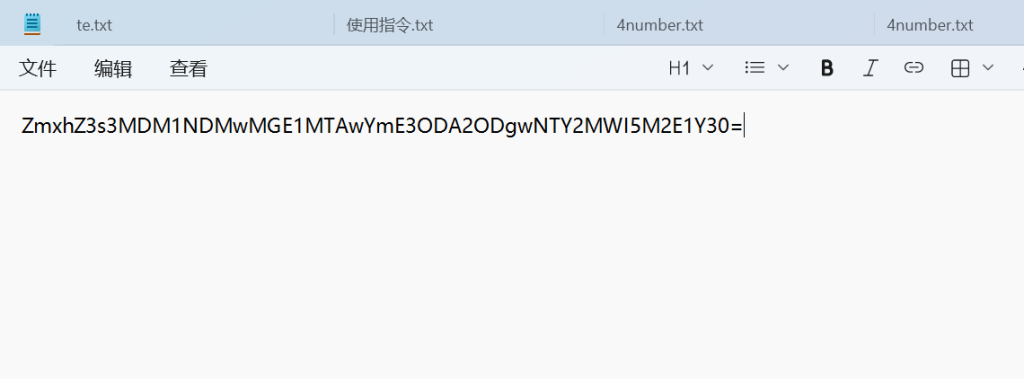
Base64解码:
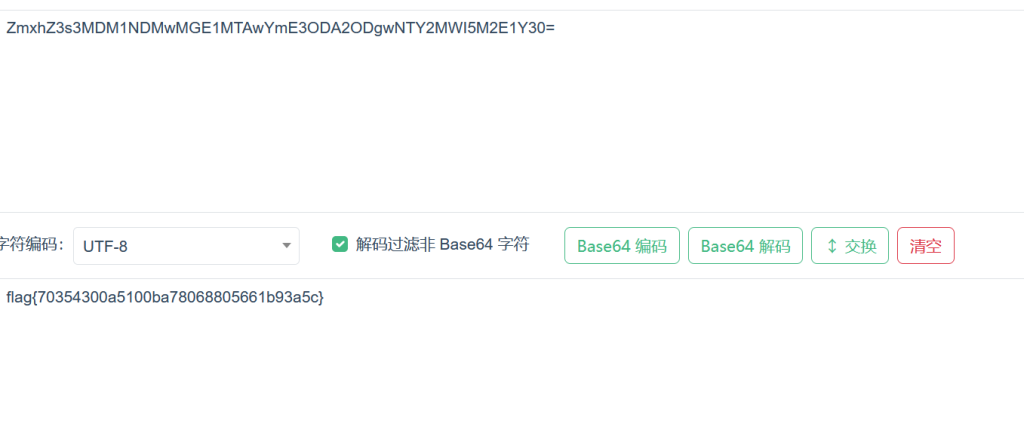
得到:
flag{70354300a5100ba78068805661b93a5c}文件中的秘密
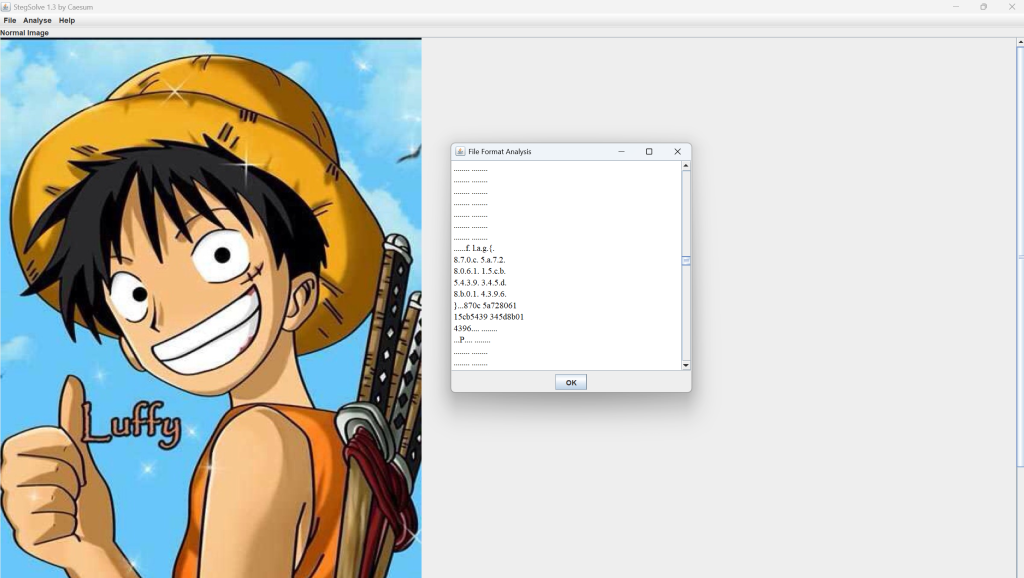
用Stegsolve打开,得出flag
被嗅探的流量(流量分析)

输入过滤器
http.request.method=="POST"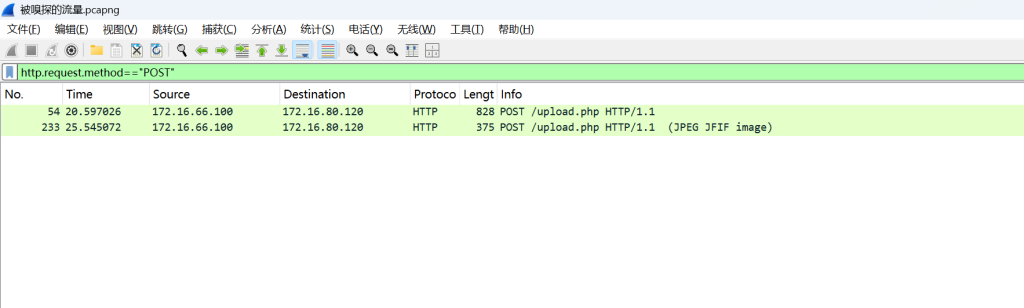
看这两个数据包的flag字样,第一个没有,第二个有
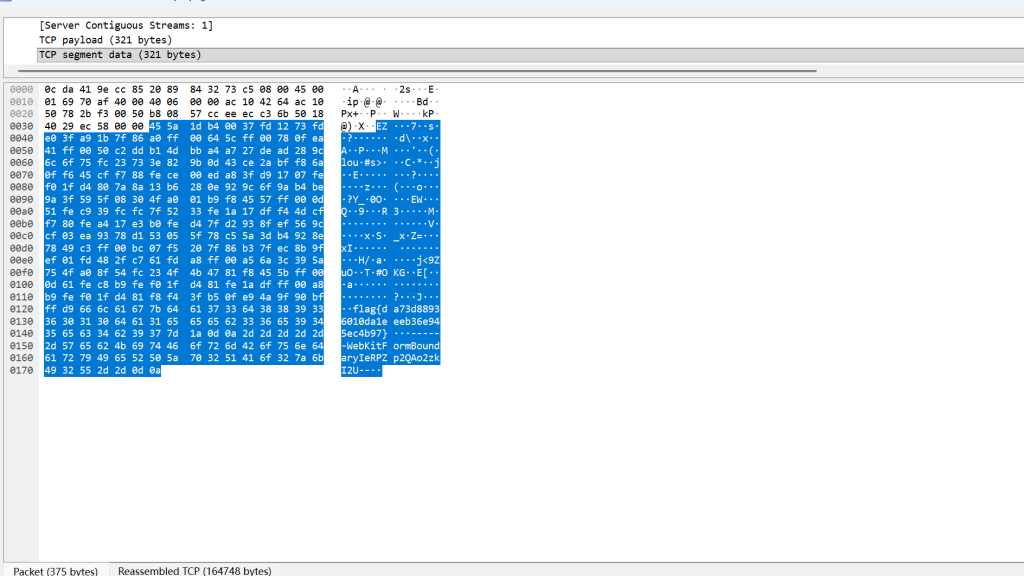
flag{da73d88936010da1eeeb36e945ec4b97}zip伪加密
简单的zip伪加密
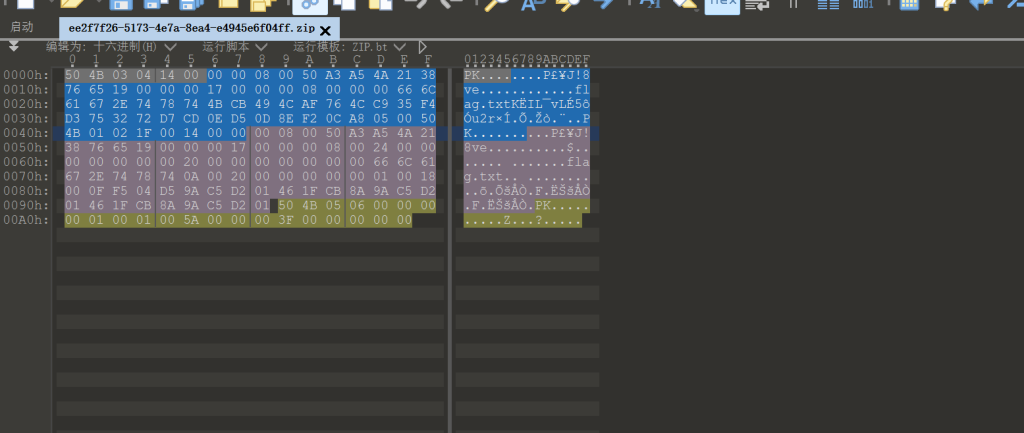
两处09改为00,解压后就是flag.txt
flag{Adm1N-B2G-kU-SZIP}
-----------------------------------------------------------------
知识点:未加密:
文件头中的全局方式位标记为00 00
目录中源文件的全局方式位标记为00 00
伪加密:
文件头中的全局方式位标记为00 00
目录中源文件的全局方式位标记为09 00
真加密:
文件头中的全局方式位标记为09 00
目录中源文件的全局方式位标记为09 00
ps:也不一定要09 00或00 00,只要是奇数都视为加密,而偶数则视为未加密------------------之后会选择有难度或者有收获的题进行wp记录-----------
数据包中的线索
给了个流量包
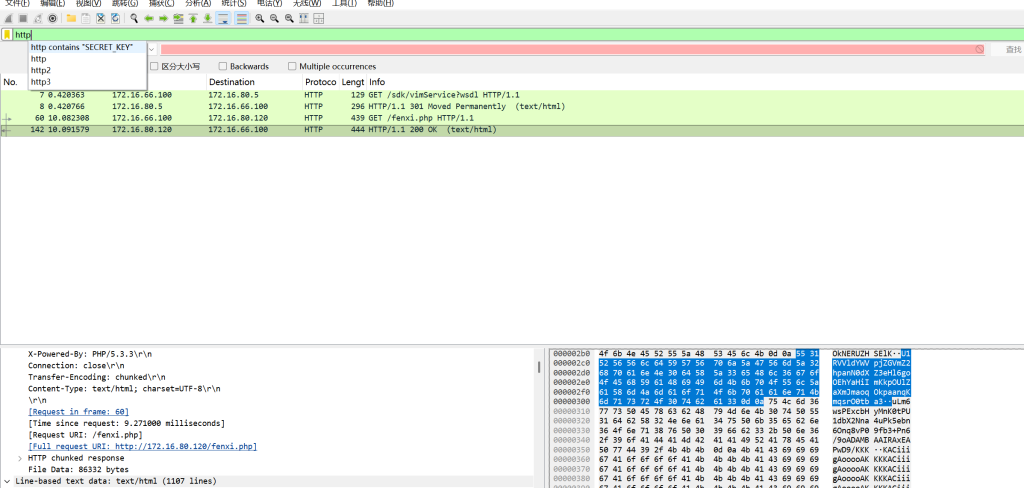
搜索http,并追踪流
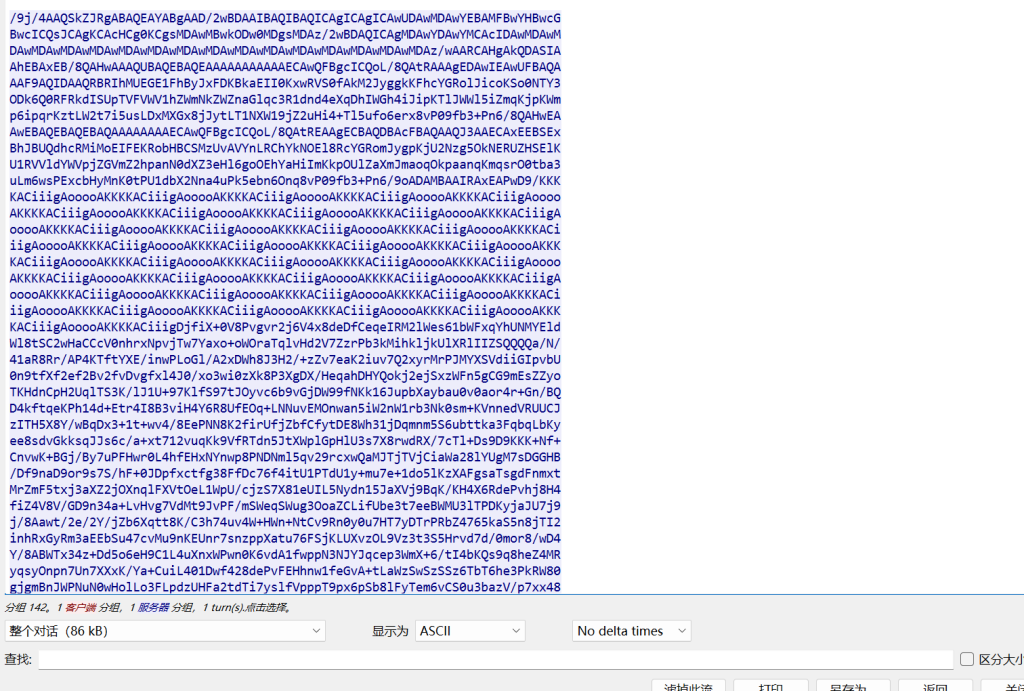
发现这个里面有一长串奇怪的编码,看到编码最后有个=,猜是Base编码
拿去cyberchef
出了个图片,这个图片带有flag
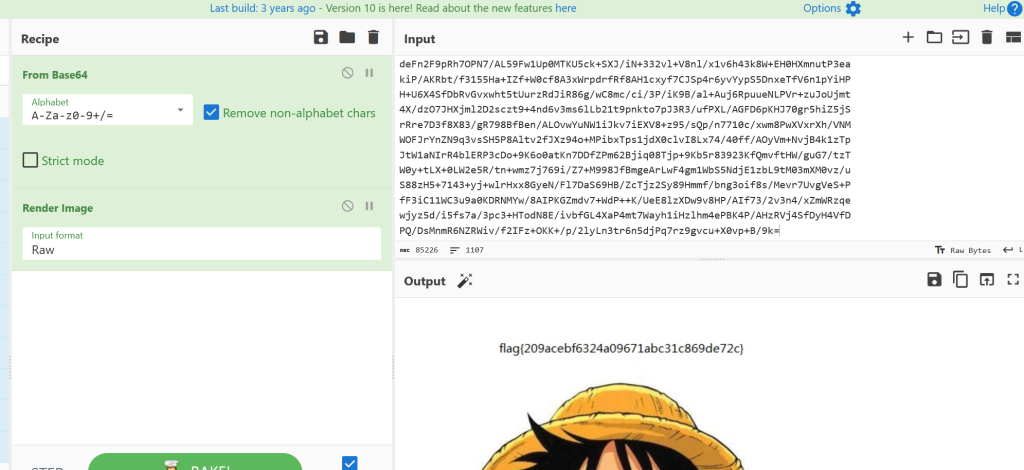
flag{209acebf6324a09671abc31c869de72c}另一个世界
所给一个jpg,文件尾巴有01编码
这个用cyberchef的From Binary直接解出
知识点:0/1编码------------->Binary编码
flag{koekj3s}神秘龙卷风
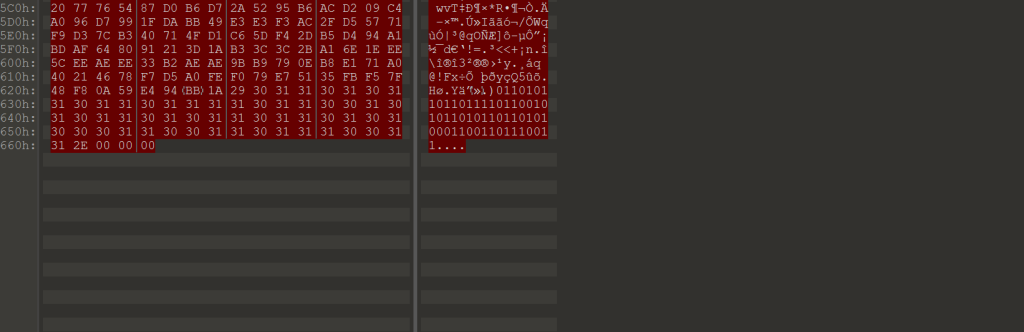
给了个rar,检查不是伪加密,直接爆破,里面是一个txt文件
+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++
+++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++++++
+++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++
+++++++++++++++++++++++++++++++++++++++++++++++
++++++++++++++++++++++++++++++++++++
++++++.>++++++++++++++++++++++
++++++++++++++++++++++++++
++++++++++++++++++++++++
++++++++++++++++++++++
+++++++++.>+++++++++
++++++++++++++++++
++++++++++++++++++
++++++++++++++++++
++++++++++++++++++
++++++++++++++++++++
++++++++++++++++++++++.>
+++++++++++++++++++++++++++
+++++++++++++++++++++++++++++++
+++++++++++++++++++++++++++++++++++++
++++++.>++++++++++++++++++++++++++++++++++
++++++++++++++++++.>+++++++++++++++++++++++++++
++++++++++++++++++++++++++++++++++++++++++++++++++++
+++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++
++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++
++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++
+++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++
+++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++
+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++
+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++
++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>
+++++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++.>
直接brainfuck解码
得到flag
知识点:+++>.>类似符号为brainfuck编码
面具下的flag
给的jpg---》提取出zip,得到vmdk文件----》虚拟机处理(brainfuck和Ook!编码)
知识点:
.vmdk 文件当您创建一台新虚拟机并指定其硬盘大小时,您就是在创建一个 .vmdk 文件。
使用kali Linux,自带的7z解压可以看到隐藏的文件7z x flag.vmdk -o"/home/kali/Desktop/"
Comments NOTHING